What is the RFC 3161 protocol?
RFC 3161, sometimes referred to as the Time-Stamp Protocol (TSP), is an open standard that enables a timestamping authority (TSA) to produce a timestamp token linking a cryptographic fingerprint (hash) of data to a given moment. This token is digitally signed, ensuring that it has not been altered and that the data did indeed exist at the stated time.
Whereas in the physical world the prior existence of a document could be established by a seal or a handwritten signature bearing a legible date, RFC 3161 provides a cryptographic equivalent. A timestamp token delivers strong cryptographic evidence that a given data set existed at a specific point in time, rendering any alteration detectable and ensuring its integrity over time.
How does RFC 3161 timestamping work?
Timestamping under RFC 3161 is based on an exchange between a client and a TSA. The process begins with the generation of a digital fingerprint of the data (a hash). This fingerprint is sent to the TSA, which incorporates it into a timestamp token signed using a secure private key. The token notably contains the fingerprint, the certified date and time, and a unique identifier ensuring the uniqueness of the transaction.
Subject to the availability over time of the necessary validation elements (certificates, revocation information, algorithms), the token may remain verifiable even after the TSA certificate has expired or the trust chain has evolved. This property is particularly significant where documents must be retained or produced years after their creation.
A standard for strengthening digital evidence
Within the electronic evidence ecosystem, RFC 3161 timestamping is not a superficial feature: it is a structuring legal and technical component. It addresses two fundamental questions for digital trust: “When did this data come into existence?” and “Has it been altered since?”
This form of timestamping does not rely on a simple date embedded in a file, but on independently verifiable cryptographic evidence. This is especially relevant for documents subject to statutory retention requirements or regulatory obligations.
In contexts such as long-term archiving or extended digital signatures (for example, software or electronic instruments), an RFC 3161 token ensures that evidence remains enforceable even after the expiry of the original certificates.
RFC 3161 and modern trust chains
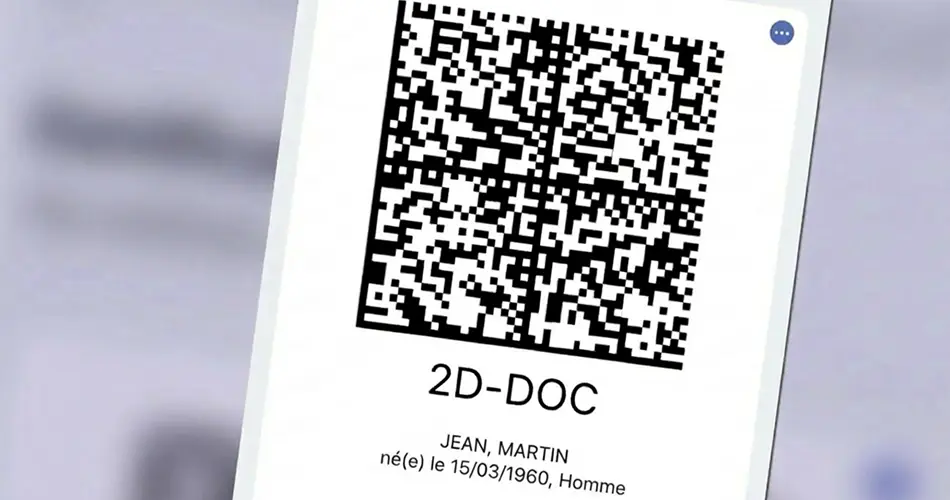
The application of RFC 3161 naturally forms part of trust service architectures compliant with eIDAS or other regulatory frameworks. In such environments, qualified timestamping acts as a digital notary, providing a time seal that integrates with qualified electronic signatures, electronic archives and other structured digital evidence.
Timestamping authorities implementing the RFC 3161 protocol rely on stringent requirements relating to time management, the protection of cryptographic keys and transparency through timestamping policies.
When combined with a trust framework such as the eIDAS Regulation, this level of rigour enables timestamping to be afforded recognised evidential value in audit and legal contexts.
What criteria should be considered when integrating timestamping (RFC 3161) into evidential processes?
In practice, integrating timestamping (RFC 3161) does not consist in simply “activating a timestamp”. It requires structuring an evidential chain in which timestamping forms a coherent component alongside other elements (traceability, retention, reproduction). To preserve the evidential weight of an RFC 3161 token, several aspects must be defined at the design stage.
First, the timestamp must apply to a cryptographic fingerprint calculated in a reproducible manner, over a clearly defined documentary scope (single document, file, annexes, metadata).
Secondly, retention periods and long-term verification arrangements must be anticipated: validation policies, preservation of certificate chains, algorithm management and, where appropriate, suitable renewal or evidential archiving mechanisms.
Finally, operational value depends on the ability to reproduce the evidence (token, associated data, event logs) in a form that is intelligible and usable in an audit or dispute context.
Typical use cases and points of attention for legal departments
Within organisations, timestamping (RFC 3161) is typically used where disputes relate to a reliable date and absence of alteration: filing a contractual version, establishing prior existence of a creation, tracing consent, or building an audit trail in the context of a regulatory filing or a sensitive workflow. The evidential logic remains the same: demonstrating that specific data existed at a given time and that the version subsequently produced is identical to the one timestamped.
Two points of attention arise frequently.
- The first concerns “chaining”: an isolated timestamp proves a state at time T, but the strength of the evidential file depends on continuity between events (creation, transmission, acceptance, archiving).
- The second concerns governance: who triggers the timestamp, under which rules, with what guarantees as to the integrity of source systems, and how these elements are documented. In contentious proceedings, it is often these architectural and procedural choices that determine how the overall reliability of the system is assessed.
Conclusion
RFC 3161 provides a standardised mechanism for producing a signed timestamp token that is independently verifiable and capable of establishing the prior existence of a digital fingerprint. For legal departments, the issue is not solely technical: it is to ensure that timestamping is embedded within a retention and reproduction chain compatible with audit requirements and evidential standards in the event of dispute. Where implemented within an appropriate trust framework, in particular one compliant with the eIDAS Regulation, RFC 3161 timestamping becomes a tool that can be relied upon to secure evidence over time, without dependence on simple file metadata or local system clocks.
Disclaimer
The opinions, presentations, figures and estimates set forth on the website including in the blog are for informational purposes only and should not be construed as legal advice. For legal advice you should contact a legal professional in your jurisdiction.
The use of any content on this website, including in this blog, for any commercial purposes, including resale, is prohibited, unless permission is first obtained from Evidency. Request for permission should state the purpose and the extent of the reproduction. For non-commercial purposes, all material in this publication may be freely quoted or reprinted, but acknowledgement is required, together with a link to this website.