Key points to remember about document fraud risk
- The risks of document fraud can be many: financial, reputational, legal…
- Risk control is based on three guarantees: integrity, date certainty and origin.
- Prevention becomes truly effective when evidence is integrated into the flow, rather than added after the fact.
- Qualified electronic time stamping benefits from a presumption of date/time and integrity of associated data.
- In auditing and litigation, the difference lies in restitution: producing legible, correlated, intelligible evidence.
The different types of risk
“Document fraud” is often confused with “false document”. However, in an organisation, the issue is not simply the existence of a falsified document: it is the occurrence of concrete damage, often immediate, and rarely isolated.
- Financial risk: undue payment, double payment, additional costs linked to a service never carried out, loss of margin, even immobilisation of cash flow while the anomaly is identified and the flows secured.
- Risk of business disruption: blockage of a purchasing process, suspension of a delivery, manual reconstitution of a file, urgent internal mobilisation (finance, legal, IT), with a direct effect on lead times and service quality.
- Reputational risk: loss of partner confidence, loss of credibility in the event of an audit, or the perception of poor governance when the company cannot simply explain “which version was the right one” and when.
- Legal and compliance risk: contesting a decision, taking the company to court for negligence, difficulties in responding to a supervisory authority, and, in certain sectors, loss of eligibility for contractual or industry schemes.
This impact-based approach has a practical advantage: it enables flows to be prioritised not according to the sophistication of the fraud, but according to the real cost to the organisation (loss, downtime, disorganisation, external exposure).
Fraud risks by sector
Mapping by function is often more effective than a “document type” approach, because it starts from usage. In purchasing/finance departments, the risk of fraud is concentrated on documents that trigger an operation: supplier creation, payment, updating of contact details, validation of an expense. In HR, exposure comes from incoming documents, transmitted outside workflow and then integrated into a file: they are difficult to attribute and date. In the legal and sales functions, disputes frequently concern versions: appendices, clauses, pricing schedules, proof of acceptance. On the operations side, the risk increases with volume, subcontracting and the field (mobile), as documents become attestations of a fact (delivery, intervention, acceptance).
Purchasing and finance
The classic pattern is well known: an “actionable” document circulates (RIB, invoice, order form), then an element is modified the moment it leaves the controlled chain. The more the flow depends on e-mail or shared spaces, the more discreet the substitution. The consequence is not just loss: it’s the effort involved in proving that the original version of the payment order has been found, who transmitted it, and that it has not been altered.
RH
In HR, the risk often takes the form of a recomposed file: a receipt arrives in a photo, a PDF is renamed, an item is replaced “for updating”. The legal difficulty arises when the company has to prove the origin and date of receipt (or date of issue) of a sensitive document, in a context of conflict or control.
Legal and commercial
Fraud is rarely frontal: it takes the form of a dispute (“this is not the annex transmitted”, “the clause has been added”, “acceptance has not taken place”). The risk is greatest when the opposable version has not been stabilised at the right time, or when proof of acceptance is based on traces that are difficult to contextualise.
Construction, supply chain, operations
In the supply chain and the construction industry, documents attest to the facts: quantity delivered, weighed, received, conformity. Fraud and disputes are fuelled by volume and intermediaries. In certain supply chain contexts, the requirement for traceability transforms proof into an operating condition, and the fragility of proof becomes a risk of operational non-compliance.
E-commerce and platforms
In the e-commerce sector, the risk often takes the form of an external challenge (controls, requests for justification) relating not only to PDFs, but to data: histories, event logs, proof of publication. The legal question becomes: can the organisation quickly produce coherent, unalterable proof over a given period?
Reducing the risk of fraud: controls, governance and proof by design
Reducing risk does not mean “over-securing” every document. It means securing what, if challenged tomorrow, would generate disproportionate legal costs. Organisational measures form the first stage: version repository, imposed channels for sensitive documents, roles and access rights, double validation for certain events (change of bank details, modification of appendices, issue of certificates). However, these controls reach a limit as soon as the document circulates between several tools or actors.
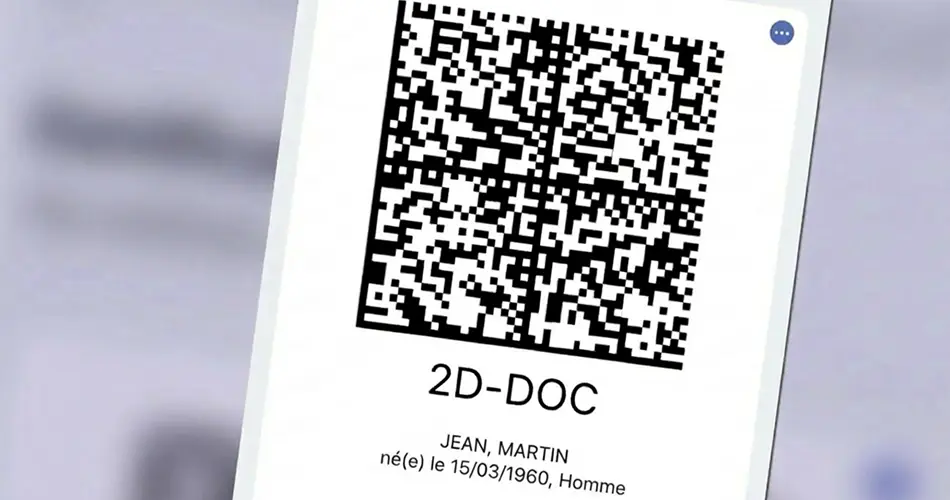
This is where “proof by design” comes into play: integrating guarantees into the flow that stabilise the version and enable fraud to be detected. The three structural guarantees are integrity, date certainty and origin. In practice, these guarantees are based on two instruments that are particularly useful in organisations: qualified electronic time-stamping and electronic stamping.
- Integrity: being able to demonstrate that content has not been modified. Qualified time-stamping anchors a document’s hash to a specific date and time; any subsequent modification renders the hash inconsistent with the timestamp token.
- Date certain: to anchor a state/version at a specific point in time, in an opposable manner. In the European Union, a qualified electronic timestamp benefits from a presumption on the accuracy of the date and time it indicates, as well as on the integrity of the data to which it refers (eIDAS regulation, art. 41[1]).
- Origin: verifiably attribute the document to the issuer, in particular the legal entity. The electronic seal plays a role comparable to that of a company stamp: it links a document to the identity of the issuing organisation and indicates any alteration, thus reducing the risk of version substitution in document flows (attestations, certificates, official statements, contractual documents).
Preparing for audits and litigation: building a usable evidence file
An organisation can have multiple traces (logs, exports, e-mails) and remain fragile for lack of intelligible restitution. In auditing, as in litigation, we don’t ask for an accumulation of evidence: we ask for a coherent demonstration. A usable file of evidence must make it possible to reconstruct the chronology (who, what, when) and identify the opposable version. It brings together, in a structured way: the version of the document, integrity elements, dated events (filing, validation, transmission, acceptance), the origin of the issuer, as well as the storage logic.
Conclusion
Document fraud risk is managed less as a hunt for forgeries than as a mastery of uncertainty: knowing how to stabilise a version, establish a date, attribute an origin, and restore a chronology. The method is progressive: qualify the types of risk, map exposures by function/sector, reduce grey areas through controls and proof integrated into the flow, then prepare restitution with a view to an audit or litigation.
The challenge for a legal department is simple: to avoid discovering at the moment of disagreement that the evidence is scattered, illegible or questionable.
Sources
[1]Regulation (EU) No 910/2014 (eIDAS), Article 41 (legal effect of electronic time stamps): https: //eur-lex.europa.eu/eli/reg/2014/910/oj?locale=fr
Disclaimer of liability
The opinions, presentations, figures and estimates presented on the website, including the blog, are intended for information purposes only and should not be construed as legal advice. For legal advice you should contact a legal professional in your jurisdiction.
The use of the content of this website, including the blog, for commercial purposes, including resale, is prohibited without prior authorisation from Evidency. The request for permission must specify the purpose and extent of reproduction. For non-commercial purposes, all material in this publication may be freely quoted or reprinted, but acknowledgement is required, together with a link to this website.